Being a SharePoint developer and not a SharePoint admin, I must admit, I don’t usually take the time to examine each new Administrative Toolkit that gets released, but something in the latest release caught my eye: the “Check Effective Permissions” tool. This is part of the “Permission Reporting” solution package that you can install as part of the Administrative Toolkit. (For instructions on installing PermissionReporting.wsp, see the TechNet article about installing the Admin Toolkit.) Once you install the “Security Report” feature at the Farm level, new options are instantly available to you on the Site Settings page for each of the Site Collections in your farm.
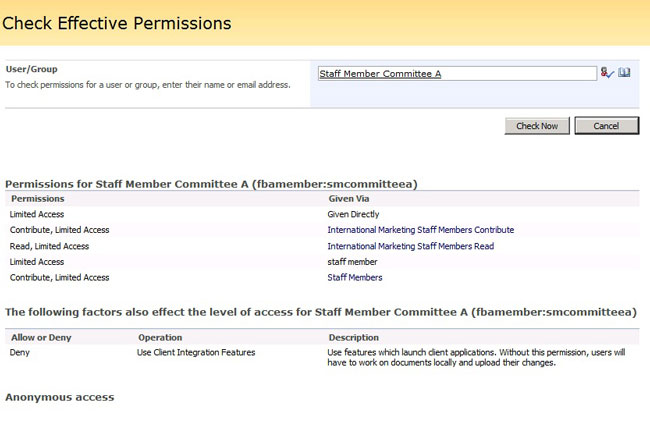
As you probably know, permissions in SharePoint tend to be more “additive” than “subtractive”, meaning you rarely deny a user rights to something; instead, a user starts out with essentially zero rights, and you gradually grant the user more and more permissions to carry out various tasks. However, this can get sticky because a user can be a member of an Active Directory group or an FBA role, and that group or role can belong to a SharePoint Group. If a user shows up in more than one group, it can be hard to know what level of permissions a user “effectively” has. Enter the “Check Effective Permissions” tool.
I like the fact that the tool takes into account FBA users and roles as well as Active Directory users and groups. It would be nice if this view gave more detailed view about item level permissions that a particular user might have other than saying “Given Directly”, but I suppose the query would have gotten ridiculously huge for this page if they had included that info here.
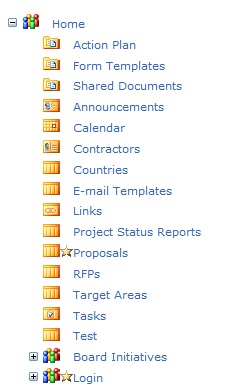
Luckily, the folks at Microsoft have given us an alternative tool that helps us view Item Level Permissions and broken inheritance. If you click on the “Compare Permissions” link in the Site Settings, you’ll be taken to a tree view for your site collection, which indicates which assets have unique permissions by showing you a “star” icon.
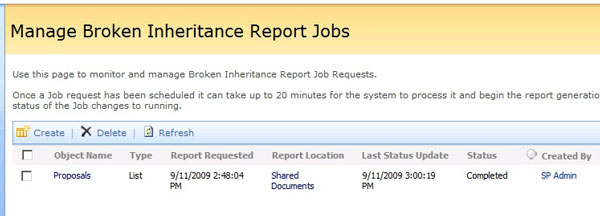
However, this tool doesn’t show you item level permissions, either. It just shows you the permissions that have been assigned to that list or site. If you want a report, you can go to the “Broken Inheritance” report page. This page allows you to generate an XML report of all the items that have broken inheritance, and which rights have been assigned to those items. The nice thing about this report is that it runs as a background process in a SharePoint timer job, so you don’t have to worry about totally bogging down your server processing or having an IIS timeout.
Here are the official help files for all three tools:
Check Permissions for a user or group
Compare Permission Sets
Run Broken Inheritance Reports
Note: I ran into some significant issues when installing the Toolkit because you need to install the April 2009 Cumulative Update in addition to SP2. Although I thought I had installed it, apparently it didn’t install correctly, and it didn’t increment the version number of Microsoft.SharePoint.dll. You can’t activate the Permissions feature (called “Security Report”) at the farm level if that version number isn’t higher than the April CU number. Take a look at the notes at the bottom of the TechNet article I mentioned in the first paragraph to see the version number you need to have to activate the Security Report feature.